Shadowy US Spy Firm Promises To Surveil Crypto Users For The Highest Bidder
The documents are among a trove related to the secret operations of Anomaly 6, a shadowy private spying firm founded by a pair of U.S. military intelligence veterans.
By Kit Klarenberg | MintPressNews.com
Leaked files reviewed by MintPress expose how intelligence services the world over can track cryptocurrency transactions to their source and therefore identify users by monitoring the movements of smartphone and Internet-of-Things (IoT) devices, such as Amazon Echo. The contents comprehensively detonate the myth of crypto anonymity, and have grave implications for individuals and states seeking to shield their financial activity from the prying eyes of hostile governments and authorities.
The documents are among a trove related to the secret operations of Anomaly 6, a shadowy private spying firm founded by a pair of U.S. military intelligence veterans.
The company covertly embeds software development kits, or SDKs, in hundreds of popular apps, then slices through layers of “anonymised” data in order to uncover sensitive information about any individual it chooses anywhere on Earth, at any time. In all, Anomaly 6 can simultaneously monitor roughly three billion smartphone devices – equivalent to a fifth of the world’s total population – in real-time.
Having previously hawked its wares to U.S. Special Operations Command, as this journalist revealed on December 6, Anomaly 6 is now using British private military company Prevail Partners – heavily involved in the West’s proxy war in Ukraine – to market and sell its product to a variety of Western military, security, and intelligence agencies the world over. This is despite the company’s own founders fearing its global dragnet could be completely illegal under national and international data protection regimes.
The company’s international surveillance reach could be more sweeping – and invasive – than even that of the C.I.A. and N.S.A. MintPress can reveal individuals, organizations, and states seeking to bypass traditional financial structures and systems loom prominently in Anomaly 6’s mephitic crosshairs, and spying on their transactions is a pivotal component of its sales pitch to government and private clients. This Orwellian technology leaves cryptocurrency users the world over nowhere to hide.
Who Watches The Watchers?
Ever since Bitcoin’s launch in 2009, anonymity has been an absolutely fundamental tenet of cryptocurrency. The ability to make and receive payments incognito through a secure, decentralized platform without needing to register a named bank account, or even interact with established financial gatekeepers at any stage, was and remains a unique selling point for the asset.
The principle of anonymity is taken so seriously by crypto practitioners and aficionados alike that industry platforms are graded according to their levels of privacy. Many crypto entrepreneurs, some of whom manage hundreds of millions of dollars for clients, conduct business without ever disclosing their names, or any identifying information at all. Venture capital firms have even invested vast sums in crypto ventures with wholly pseudonymous founders, an unprecedented sectoral development.

In recent years, however, there have been several clear indications that cryptocurrency anonymity is under significant threat, and indeed could already have been mortally compromised by the U.S. intelligence apparatus. In June 2021, it was revealed that the F.B.I. had successfully traced and recovered $2.3 million in Bitcoin extorted by hackers from Colonial Pipeline in a ransomware attack, which had shut down the company’s computer systems, causing fuel shortages and a spike in gas prices.
U.S. officials declined to reveal how they tracked where the ill-gotten funds had ended up, and identified the ultimate owners of 23 separate cryptocurrency accounts belonging to DarkSide, the hacking collective responsible for the cyber-attack, although public statements by C.I.A. director William Burns in December that year may provide a clue. Speaking at a Wall Street Journal summit, he acknowledged that his Agency was engaged in “a number of different projects focused on cryptocurrency.”
“This is something I inherited. My predecessor had started this,” he said. “Trying to look at second- and third-order consequences as well and helping with our colleagues in other parts of the U.S. government to provide solid intelligence on what we’re seeing as well.”
While it’s certainly true that cryptocurrency’s anonymity is attractive to criminal elements and terrorist groups, there are a wide variety of entirely legitimate reasons for seeking privacy in financial transactions, and preventing regulators, big banks, and governments from keeping an eye on what one is doing.
For example, political and social movements of every stripe in all corners of the globe have embraced the asset, as they can be financially supported from overseas without any paper trail being left at either end. In turn, activists can send money to each other and make purchases in secret, and organize events and construct local and international support networks, leaving authorities none the wiser.
In Venezuela, cryptocurrency has provided vital respite to an entire country, as crippling U.S.-led sanctions have in recent years deprived both its government and citizens of access to, and the ability to buy, even basic necessities, including food and medicine. The national currency’s value reduced to almost zero, crypto transactions offer a literal lifeline by which goods and services can be accessed, and import and export restrictions imposed by Washington circumvented.
‘Patterns of Life’ &‘Bed Down Locations’
A February 2021 U.N. special rapporteur report on the impact of American sanctions on Venezuela ruled they were “collective punishment,” and Caracas lived on just 1% of its pre-sanctions income. The previous March, Alfred de Zayas, formerly an independent expert for the United Nations Human Rights Council, calculated that over 100,000 Venezuelans had died as a result of the restrictions.
Despite this monstrous human toll, and countless calls from prominent rights groups and international institutions to end the suffering, Washington rigidly enforces the sanctions regime, and seeks to harshly punish any individual or organization helping Caracas skirt restrictions. While measures have eased slightly following Russia’s invasion of Ukraine, the Stateside prosecution of Colombian businessman Alex Saab, abducted from Cape Verde in October 2020, for selling food to the Venezuelan government is ongoing.
Saab could be soon joined in the dock, if Anomaly 6 has anything to do with it. One of the company’s leaked sales presentations provides several case studies showing how its spying technology can be used by security and intelligence services to “derive understanding of the actions of individuals associated with sanctions violations.”
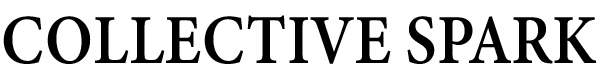
By homing in on the location of the Venezuelan government’s sanctioned cryptocurrency exchange, the National Superintendence of Cryptoactives and Related Activities (Sunacrip), which manages all crypto activities in the country, Anomaly 6 identified two specific IoT devices “which show the value of the A6 dataset in this endeavour.”
Scouring data generated at the site back to January 1, 2020, Anomaly 6 found thousands of signals emitted by IoT devices and smartphones. From there, it “built out the pattern of life for the devices in that search” – in other words, the locations device owners travelled to and from, when, and where they lived. In all, these devices produced “over 593,374 geographic points of reference”, in Argentina, Colombia, and Venezuela.
From this amorphous corpus, Anomaly 6 identified one device with “a unique travel pattern which makes it worth further investigation.” In particular, its movements indicated a “very well-defined pattern of life in and around Caracas” – although the company professed to be “much more interested in its travel to the Colombian border in the Cúcuta/San Antonio del Táchira border area.”
That Anomaly 6 was able to track this device while in flight was said to highlight a “unique aspect” of its dataset. The device “took a less than seven hour trip from Caracas to San Antonio del Táchira (Juan Vicente Gómez International Airport) which landed (or was on final approach at 0923 on 23 Feb).”
“With less than 10 flights a day on average to this airport (pre-Covid-19), it would not be difficult to ascertain a short list of personalities of interest with access to Venezuelan passenger name records,” Anomaly 6 bragged. “Additionally, we can see that this device transits to the border crossing locations in the short time it was located in the area.”
This border area was of note for Anomaly 6 as, “according to open source reporting, historically, Venezuelans have used border areas for cash pickup/drops to skirt sanctions put in place by the international community.” Such activities “provide access to hard currency to actors and governments which have been cut off from U.S. dollar trading platforms.”

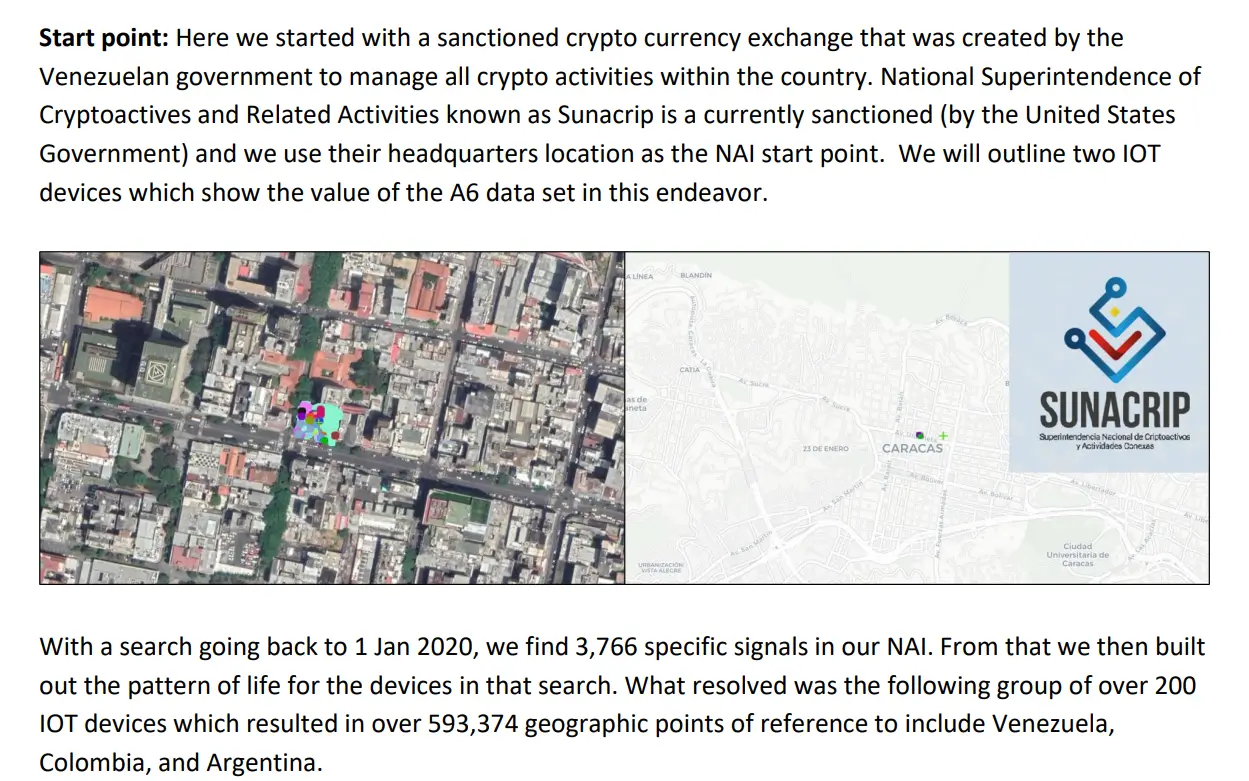
A “second device of interest” was found to have travelled to Medellín, Colombia, and its “pattern of life” indicated its owner had “connections to the financial/banking environment.”
“Both of these devices exhibit [patterns of life] that warrant further exploration, especially when combined with fact [sic] they have been located at the Sunacrip HQ,” Anomaly 6 concluded. “Further investigation can find bed down locations as well as other insights for business locations, international travel, and other device co-location.”
The Devil Turns Around
Due to a highly successful mainstream media campaign over many years to demonize the government of Venezuela, and by extension its people, it is likely some American citizens will be entirely unsympathetic to Caracas’ plight, and approve of efforts to prevent the state bypassing sanctions. However, the ease with which Anomaly 6’s tools of mass surveillance could be domestically deployed, and the likelihood they already have, should give them pause.
As I revealed in my initial report, Anomaly 6 can identify U.S. smartphone users by name, address and travel history. Another leaked sales presentation details how by linking a single anonymous individual’s smartphone signal recorded in North Korea to a network of hotels, schools, and other sites, the company determined with pinpoint accuracy their identity, marital status, where they worked and lived, the names of their children and the schools and universities at which they study, and more.
Such capabilities would no doubt be of much interest to the C.I.A. and N.S.A. – both of which are in theory prohibited from spying on U.S. citizens, but have been recurrently embroiled in controversy for engaging in such activity.
Concerningly, it has been revealed that the C.I.A. for many years sought to bulk collect international financial data in service of tracking the Islamic State’s funding sources, and incidentally vacuumed up voluminous quantities of sensitive information on U.S. citizens in the process.
Heavily redacted records related to the connivance were unearthed due to pressure from senators Ron Wyden and Martin Heinrich of the Senate Select Committee on Intelligence. Upon reviewing the material, they wrote to U.S. Director of Intelligence Avril Haines, righteously admonishing the C.I.A. for brazenly ignoring longstanding constitutional checks and balances on the Agency’s domestic activities.
“[The C.I.A.] has done so entirely outside the statutory framework that Congress and the public believe govern this collection, and without any of the judicial, congressional or even executive branch oversight that comes with FISA collection,” they fulminated.
Anomaly 6’s services, of course, mean the C.I.A. and N.S.A. can dodge restrictions at home, without fear of landing in hot water. Other agencies permitted to monitor Americans can likewise now do so without a warrant too. And there is no reason to believe that its spying would be restricted to financial transactions, either
“Anomaly 6 data can be used in multiple use cases to support cyber intelligence and operational use end states,” the leaked crypto sales deck declares. “By utilizing multiple targeting methodologies, this data can support the building of a far superior intelligence picture that enables clients to move towards actionable end states. Fusing A6 data with other classified and unclassified data sets places the client at the forefront of the cyber mission space.”
Other leaked Anomaly 6 files openly discuss how its technology is ripe for both “counterintelligence” and “source development” purposes, and it’s not merely U.S. citizens in the firing line. The firm boasts of having spied on the movements of “devices from other friendly countries,” including members of the Five Eyes global spying network, and France and Germany.
In other words, Anomaly 6 turns every citizen on Earth into a potential “person of interest” to intelligence agencies, and thus a target for recruitment, surveillance, harassment, and much, much worse, the most intimate details of their private lives easily accessible by shady actors with a few clicks of a button, and without their knowledge or consent.
While the mainstream media is yet to acknowledge the leak of the company’s sensitive internal papers, this has all the makings of an Edward Snowden-level international scandal of historic proportions. If Anomaly 6 is to be successfully stopped in its tracks, and Western intelligence agencies prevented from egregiously violating the privacy of innumerable individuals without compunction or oversight, it will require concerted collective action from concerned citizens worldwide.
Views expressed in this article are the opinions of the author and do not necessarily reflect the views of Collective Spark.
* * *
READ MORE: China’s Shipbuilding Capacity More Than 200 Times Greater Than US: Navy Intelligence Slide
Liked it? Take a second to support Collective Spark.
We’d love to hear from you! If you have a comment about this article or if you have a tip for a future Collective Spark Story please let us know below in the comment section.